Clef – a magical 2 Factor Authentication (2FA) for WordPress
13 December 202123 June 2016 | Software
Why is 2 factor authentication (2FA) necessary?
We live in a world with increasing digital crime, a world in which the amount of internet fraud is ever increasing, issue that worries those in charge with database security. The classic one factor authentication has been proven weak, even with the latest attempts at forcing the setup of strong passwords and heavy hashing.
The Privacy Rights Clearinghouse has been maintaining a database of security breaches since 2005. This is a searchable database that allows users to easily track the number of data breaches. While the database contains only breaches made public, it is still a good source to analyze the trends in breaches over the years.
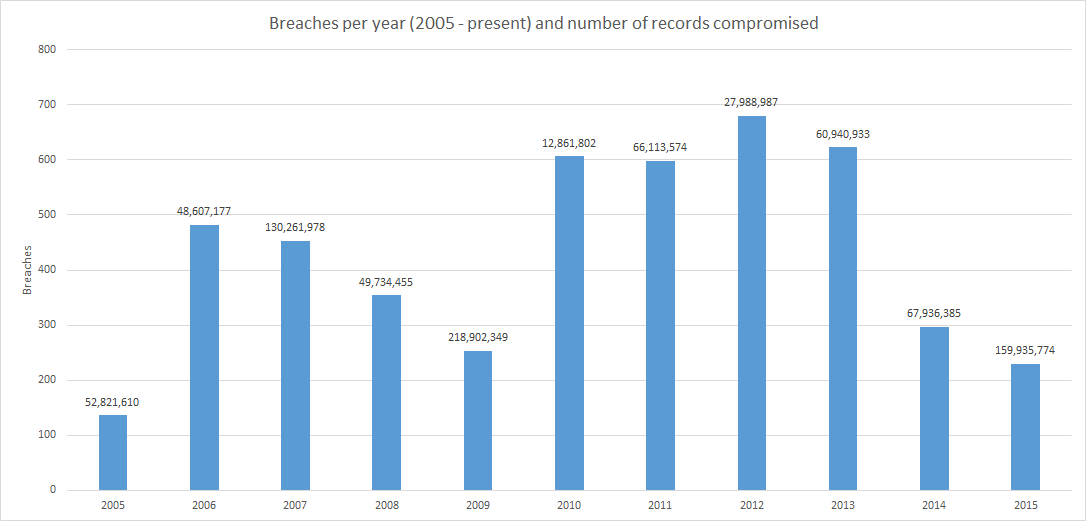
According to the 2016 Data Breach Investigations Report published by Verizon, 63 percent of the 2,260 confirmed data breaches in 2015 involved leveraging weak, default or stolen passwords.
This number confirms that it has become easier for criminals to gain access to both personal and financial private data. Clearly, the one factor authentication has failed users over and over again.
2FA. What it is and how it works?
2FA offers an extra layer of security besides a username and a password. With 2FA enabled, the user must provide something he/she knows (credentials, usually username and password) and something he/she has (smartphone, key generator, card, etc.) to authenticate.
2FA in WordPress
WordPress if a very popular CMS that stands behind over 74 million websites. That is about 19% of all websites (source). Since it is open-source, its popularity will almost certainly soar in the upcoming years. The increased popularity makes the platform a major target for hackers, who can and will exploit its security breaches. A great majority of the WordPress sites still use one factor authentication, which comes by default with the platform, so you can imagine the degree of data frailty the site owners and end-users must cope with.
For a WordPress site the users themselves set up their passwords and you, as site administrator, would hope they are unique and safe. To make things worse, these passwords get stored in a vulnerable database. It is said that hackers can crack 90% of WordPress passwords in 24 hours (source).
Luckily, 2FA plugins for WordPress are readily available, of which some of the most popular are:
- Google Authenticator
- Authy
- Clef
Without any doubt, each of these solutions has its advantages and disadvantages in their fight against common hacker attacks:
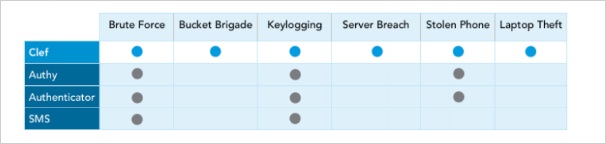
The perfect solution should combine the best features of several plugins. Of the four plugins listed above CLEF is the closest to achieving this goal.
Clef – the “magical” 2FA
The following quote from Clef’s homepage caught my attention:
“With Clef, the often painful process of logging into a site feels, admittedly, a little bit magical“ (Nicole Perlroth, Cybersecurity & Privacy, NYTimes).
After trying Clef myself, I realized there is some truth in this statement.
By using Clef, you create a digital key that generates a new signature every time you log in. This never leaves your phone and when you sync it with Clef Wave you can identify yourself by sending your signature (source). With all the important details distributed to your phone, nothing in the Clef database can compromise your identity.
Making the magic work requires the following steps:
1. Access your website’s login page through Clef

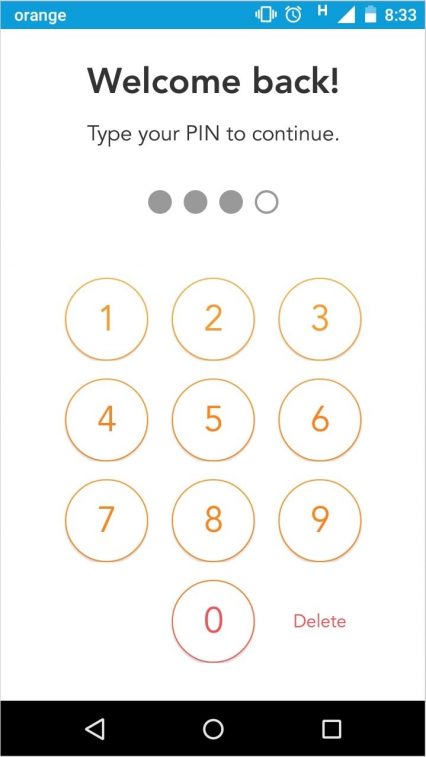
2. Start your Clef mobile app and login using the PIN chosen when registering
3. Sync the Waves and witness the magic
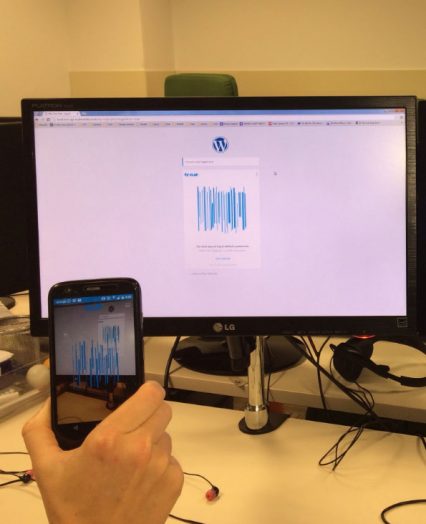
4. Your digital signature is sent to Clef
5. Clef verifies the signatures and connects to the site’s server using OAuth 2.0
6. You’re logged in!
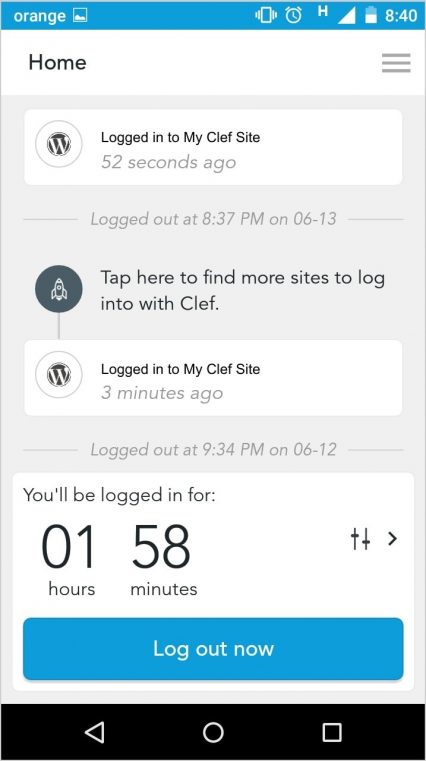
Clef not only gives a little „color” to a dull process, but also contributes to the improvement in security through its 2048 bit key (that would take the average hacker about 6.4 billion years to break). When creating a new account with Clef the users need to provide a 4-digit PIN for their device, which will be tied physically to the device. To get their hands on the PIN hackers would need to gain possession of the corresponding device. These weapons, together with the ability to limit the number of login attempts from a certain IP and remotely inactivate lost devices address, address the old problem of brute-force hacker attacks.
Sign-out from the user’s phone comes in handy when the user’s computer on which they are currently logged in via Clef gets stolen. Last, but not least, not storing account information makes Clef safe from keyloggers.
The complete list of methods used by Clef to protect its users against specific types of hacker attacks can be seen here.
Clef is a 2FA authentication solution that not only works with WordPress but can also be integrated with Ruby, Python, PHP, Rails.
141000+ sites are already integrating Clef (source). Is this the future of login? I don’t know, but it’s definitely worth giving it a try.



